
Did you hear about the latest major cybersecurity breach that disabled a public company?
“Which one?” you ask.
Take your pick.
Cyberattacks are the new weapons of mass destruction for businesses, and for society in general. One category of attacks – ransomware – has doubled since last year. The latest Sophos research concludes that the average total cost for a business to recover from a ransomware attack is 10 times the average ransom payment. Paying the ransom immediately may sound worth it, but 92% of organizations that pay ransomware don’t get all their data back.
This matter isn’t limited to the private sector and has risen to the level of national security concern. There’s growing concern within the intelligence community that foreign governments will cyber-invade financial institutions – not to steal money, but to pollute, destroy, and manipulate data. Cyberattacks by foreign intelligence services designed to create chaos in recordkeeping, transaction precision, and currency valuations could disrupt and destroy the public trust to such a degree that the stability of the entire financial system may come into play.
Role for Governments
There are actions the United States and European Union can take in the short term, like adding new requirements for technology vendors. Major vendors like Microsoft and Salesforce – which have large, lucrative contracts with governments – will likely be required to encrypt government data, preserve more digital records, notify their government customers about breaches, and allow government officials to review more intrusions.
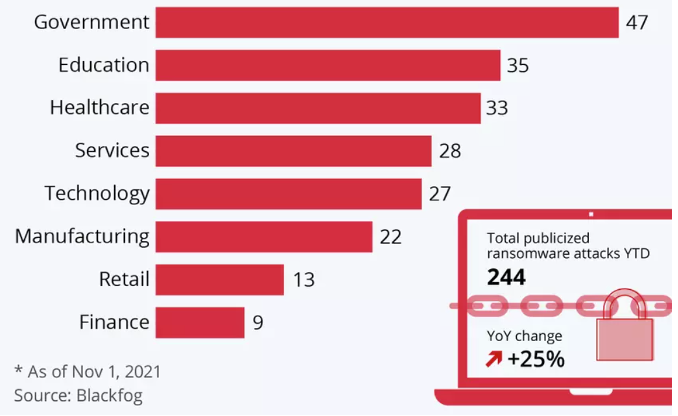
A Statista chart shows top sectors affected by publicized ransomware attacks worldwide, January-November 1, 2021.
Unlike the nations of Western Europe, the U.S. does not have a single, comprehensive privacy law. Nor does it have an agency charged with administering such a law. Biden administration activities in this area will probably be consistent with Vice President Kamala Harris’ privacy efforts in her former role as attorney general of California, which focused on protecting digital content, patient control over healthcare data, and the use of facial recognition technology in public places.
The European Commission will continue to levy large fines. Both the EC and U.S. are bound to shift the focus from blaming hacked companies to apprehending the hackers. Governments will provide law enforcement and diplomats with more resources, capabilities, and knowledge to publicize, apprehend, and bring to justice the perpetrators of cyber crimes. This strategy includes offering large rewards for information that helps punish hackers and making it more difficult to transfer funds using cryptocurrency.
More To Be Done
There are three steps the federal government, and every organization, can take – both defensive and offensive – to meet the challenge of ransomware and other attacks.
- Develop isolation tools so criminals cannot reach across software applications and systems, arbitrarily change things, and then demand that ransom be paid. Isolation is a security and reliability tool, enabled by opacity. Opacity means that software can't reach across the boundary and arbitrarily change things on the other side. We need to further develop and utilize software to isolate packages, systems, and system users from each other.
- Establish a Global Center for Threat Control that provides effective measures against widespread ransomware attacks. The center should foster intelligence-driven approaches in order to better anticipate cybersecurity threats. Governments should require sharing of information about breaches on a virtual platform and mobilize “rapid reaction teams" of cybersecurity experts to respond to incidents. We would all benefit from the learning curve. It could alleviate the burden of formally reporting incidents while simultaneously fostering the sharing of attack signatures and successful tactics, techniques and procedures in a timely manner.
- Treat cybersecurity as a management issue, not just a tech issue. The ability to quickly identify and respond to a problem will determine your organization’s ultimate recovery. It requires the right focus on three prongs:
- Risk management. Companies need to employ good risk management in order to take a broader view to ensure proper oversight of all facets related to the management of cybersecurity.
- Cyber wellness. What is needed is a proactive approach for employees with cybersecurity, just like physical wellness programs, in which the company takes an active approach promoting good cyber hygiene.
- Strategic alignment. Cybersecurity needs a more impactful managerial approach that connects it with business decision-making to impact business outcomes. Cybersecurity needs to be viewed as a growth enabler that creates a competitive advantage.
Think about it: Technology pervades all operations today – from how a business runs to how it delivers value and succeeds. But we forget that technology is also a threat to all these aspects. We need to be much more proactive in defending ourselves, our businesses, and our countries.
David X. Martin is an expert legal witness, board director, and adviser on cybersecurity and risk management. He is the author of CyRM: Mastering the Management of Cybersecurity (CRC Press, April 2021).