Unprepared, unaware, confused, bewildered - these are reactions we regularly encounter when discussing compliance with the Health Insurance Portability and Accountability Act's (HIPAA) Privacy and Security rules with our clients.
We at Buck conducted a survey recently to discover how prepared organizations are to survive a HIPAA audit. The results? Some plan sponsors didn't know when their HIPAA privacy, security, and breach notification policies and procedures were last reviewed or when a HIPAA risk/threat assessment was performed. To quote one benefits manager: “What is that? I've never heard of it.”


She is hardly alone. Many group health plan sponsors believe that they satisfy HIPAA requirements by simply performing HIPAA training every few years or by communicating a Notice of HIPAA Privacy Practices. Or they assume that broader, more general IT risk assessments or policies will address the specific requirements of HIPAA. However, there's a lot more to compliance than that.
Costs of Being Unprepared
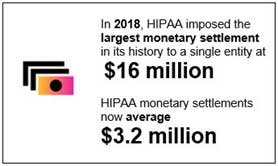
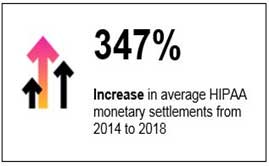
It is “risky business” to not be prepared for a Health and Human Services (HHS) HIPAA audit. Penalties for non-compliance with HIPAA have increased significantly and often amount to millions of dollars. The average monetary settlement for HIPAA infractions in 2018 was $3.2 million, and complaints, which may trigger an investigation, have been steadily rising.
In addition to the monetary penalties imposed by HHS for HIPAA-related violations, organizations can potentially incur additional costs due to:
- Investigations into the cause of the breach
- Notification letters sent to breach victims
- Imposition of identity theft protection (while not required by HIPAA, may be required by certain states)
- Creating a website/helpline for breach victims
- Remediation
- Lost business/loss of reputation
- Class action lawsuits
Look for Compliance Gaps
When we perform HIPAA compliance reviews, we usually find three critical gaps that need to be addressed: infrequent threat analysis, missing or outdated business associate agreements, and inadequate workforce training. Our recent survey substantiates these findings.
- Risk/threat analysis is not frequent enough, and not documented.
According to the survey, 42% of participants either did not know when a risk/threat analysis was last conducted or indicated that the last one was more than five years ago. HIPAA requires that a risk/threat analysis be performed “regularly.” With the rise of cyber attacks, the best practice is to perform one annually. Infrequent risk/threat analyses are one of the most common violations cited by the Office for Civil Rights (OCR), HIPAA's enforcement arm, in their analysis of the first phase of HIPAA audits.
- Business associate agreements are either outdated or missing.
OCR confirmed in its audit analysis that business associates (BAs) had more compliance issues than health plans.
Business associates of an organization are persons or entities whose activities involve the use or disclosure of Protected Health Information. BAs are directly liable for compliance with HIPAA Privacy and Security Rules. The organization is required to keep an inventory of its BAs and to have a current BA agreement (BAA) in place. In our survey,13% of the participants had not inventoried their BAs and 20% were not sure if they had a current BA inventory; 17% had some (but not all) current BAAs in place, 3% had no current BAAs, and 13% did not know if they had them.
- HIPAA workforce training has not been conducted recently.
The HIPAA Privacy Rule requires training for each staff member who has contact with Protected Health Information (PHI/ePHI) within a reasonable time after hire, and whenever there is a change in policies and procedures.
The HIPAA Security Rule requires periodic training (interpreted by many to be annual training) and whenever new guidelines or rules are issued by HHS. Workforce training is important not only for preventing breaches, but also to raise awareness of when breaches occur. Thirty-five percent of our survey respondents offered HIPAA training between one and five years ago, 13% provide training only during onboarding, and 10% did not know when HIPAA training was last provided.
As a best practice, HIPAA training should be included at onboarding for any new employee with access to PHI. Attendance at all HIPAA training sessions should be documented.
Policies and Protections
Other common gaps identified during compliance reviews include:
- Privacy policies and procedures, as well as security policies and procedures, have not been updated in many years.
- Encryption is not implemented for ePHI on removable media, network drives, or email transmissions.
- Security controls or updated virus protection is not present on personal devices used to access ePHI. BYOD (bring your own device) introduces a number of risks.
- Review of permissions for and access to PHI/ePHI is insufficient.
- Termination procedures for workforce members with access to PHI/ePHI are insufficient.
- Documented policies and procedures are not adequately communicated and therefore often not followed.
- Privacy and/or security officials not designated.
- Records of individual training completion are not maintained.
CFO Oversight
HIPAA compliance can fall under the chief financial officer.
According to a 2018 Deloitte study, 55% of CFOs claim responsibility for enterprise risk, and “CFOs said risk-related responsibilities are among the most likely to be added to their responsibility scope over the next three years.”
Understanding this complex law and its rules is the best way to prevent a breach and the only way to emerge successfully from a HIPAA Audit.
Teresa Wilkins is director, and Chris Isaacs is principal, of the Knowledge Resource Center at Buck, an integrated HR and benefits consulting, technology and administration services firm.